Let’s Encrypt is a free, public SSL certificate authority (CA) you can use to generate and automate SSL certificate renewal. I co-manage Trystack.org, a free OpenStack sandbox for the general public and our Horizon SSL certificate came up for expiration so we moved to Let’s Encrypt. Using EFF’s certbot it’s trivial to automate everything. You can do the same for your own blog or website.
Let’s Encrypt is a free, public SSL certificate authority (CA) you can use to generate and automate SSL certificate renewal. I co-manage Trystack.org, a free OpenStack sandbox for the general public and our Horizon SSL certificate came up for expiration so we moved to Let’s Encrypt. Using EFF’s certbot it’s trivial to automate everything. You can do the same for your own blog or website.
Why Let’s Encrypt
I used to always just self-sign my certificates for personal services and occasionally we would use commercial certificate authorities like Geotrust, Comodo and others but in recent years Let’s Encrypt has really gotten momentum and adoption – it’s also part of the trusted authority chain in browsers so there is really no good reason not to use it. I still self-sign certificates for personal services like Plex Media Server but I’ll be using Let’s Encrypt for everything else (including this blog).
Getting Started – Generate/Deploy SSL Certificates
If you own the domain and it listens on standard TCP 80/443 then setup is really simple using the EFF’s certbot application. These directions will cover CentOS/RHEL webservers using Apache.
First, install the EPEL repo if it’s not installed already:
wget https://dl.fedoraproject.org/pub/epel/epel-release-latest-7.noarch.rpm rpm -ivh epel-release-*.noarch.rpm
Next, install the EFF certbot application (see guide for other httpd /distribution)
yum install python-certbot-apache -y
Let Certbot Generate your Certificate
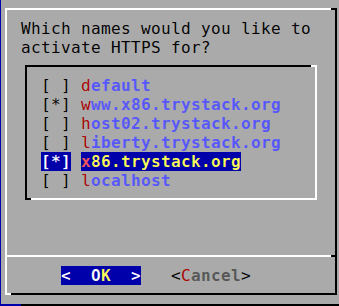
Certbot will spawn an ncurses like TUI that will give you several prompts, it should analyze your current HTTPD setup and offer to generate and renew certificates for all your virtual hosts. You can choose to only generate the certificate and copy manually but we’re just going to cover the automated method here.
Run certbot (assuming Apache webserver)
certbot --apache
Follow the prompts – it should show you your current vhosts.
Note: you can also specify specific domains using the –domains flag like so:
certbot --apache --domains funcamp.net --domains www.funcamp.net
Accept the terms.
Next it will query your hosts, and generate the certificates.
Next it will prompt you for post-deployment virtual host configuration that it can perform to update your Apache configuration with the new certificate. We just chose Easy here as we have some non-HTTPS content but choose accordingly. If you choose Secure it should do a proper HTTPS redirect for you which may be nice if you’re going from an HTTP site to an HTTPS site.
Once complete it will present you with the last dialogue, you can now restart your HTTPD server if it doesn’t take effect immediately.
Set up Automatic SSL Certificate Renewal
Let’s Encrypt has a default certificate lifespan of 90 days but you can easily setup automated certificate renewal via certbot.
We’ve chosen to just use cron for this but you could also use systemd if you wanted to. The below cron entry will check twice a day and renew your certificates if they are eligible.
crontab -e
# add entry for let's encrypt renewal 00 11,16 * * * /usr/bin/certbot renew --quiet
You can also test what would happen with the –dry-run flag prior to setting and forgetting in crontab.
certbot renew --dry-run
Saving debug log to /var/log/letsencrypt/letsencrypt.log ------------------------------------------------------------------------------- Processing /etc/letsencrypt/renewal/www.x86.trystack.org.conf ------------------------------------------------------------------------------- Cert not due for renewal, but simulating renewal for dry run Starting new HTTPS connection (1): acme-staging.api.letsencrypt.org Renewing an existing certificate Performing the following challenges: tls-sni-01 challenge for www.x86.trystack.org tls-sni-01 challenge for x86.trystack.org Waiting for verification... Cleaning up challenges Generating key (2048 bits): /etc/letsencrypt/keys/0001_key-certbot.pem Creating CSR: /etc/letsencrypt/csr/0001_csr-certbot.pem ** DRY RUN: simulating 'certbot renew' close to cert expiry ** (The test certificates below have not been saved.) Congratulations, all renewals succeeded. The following certs have been renewed: /etc/letsencrypt/live/www.x86.trystack.org/fullchain.pem (success) ** DRY RUN: simulating 'certbot renew' close to cert expiry ** (The test certificates above have not been saved.)
Limitations and Issues
Currently you need TCP 80/443 open and valid DNS entries for Let’s Encrypt to work as it uses SNI to do validation. You can work around this by using alternate validation if you cannot temporarily listen on those ports.
LE Doesn’t Pick up my vhost
Make sure that you’re combining one VirtualHost per configuration file, certbot doesn’t like when you try and combine multiple FQDN vhost domains into the same file.
Support LE and EFF
Free services like Let’s Encrypt are a real boon to the proliferation of a safer, more secure internet. I also laud the EFF for all their work towards this endeavour – both entities are non-profits and deserve your donations for this useful service and others.